Looking through the PRISM: An analysis of the NSA's Orwellian surveillance program
As someone who follows technology news pretty closely, a recent leak involving the extent of the NSA's domestic surveillance capabilities was not a big surprise to me. The passage of the Patriot Act, followed by the FISA Amendments of 2008, should have been a pretty big wakeup call to any American who takes the constitutional right to privacy, or that pesky Fourth Amendment, seriously. While many argued that it was unconstitutional no matter what, warrantless wiretapping was codified and made easier by these laws, and also by the American people's willingness to give up liberty for security - something which Benjamin Franklin warned against. But I'm not writing this post to lecture you; whether you care or don't care about these privacy intrusions, you probably won't be swayed by me. What I'm going to do is take a look at the newly leaked details about wiretapping at Verizon, Google, Facebook, and other keepers of America's private lives and examine just how extensive the NSA's abilities may be.
The first leaked document that hinted at the massive scale of the current surveillance operation was first broke by the Guardian, which orders Verizon to hand information on all calls in its system over to the NSA on an "ongoing, daily basis." No-one knows for sure whether this includes the actual content of phone calls, but at the very least this includes all of the metadata associated with every call on the Verizon network, such as who the call originated from, who its going to, how long the call was for, etc. The idea that the NSA has, theoretically, created a social interaction map of every American based on who they talk to every day is no doubt creepy, but again, can't come as a great surprise if you have paid any attention to previous leaks.
It's no secret that the NSA is plugged in to every communications backbone in the United States and monitors just about every bit and byte that goes across those fiber optic lines. The ominously named Room 641A, whose existence was exposed in 2006, is an NSA listening post set up in the same building as a major AT&T fiber optic backbone. The device mirrors all traffic which goes through the fiber backbone and routes it to the NSA, presumably for processing and analytics. The AT&T technician who exposed the room mentioned that he had knowledge of similar installations at other locations, so did we really think companies such as Verizon, or even Internet backbone companies such as CenturyLink, would be spared?
But the next leak dwarfs even the juiciest "phone line tapping" story. This whopper comes in the form of the PRISM program - a top secret operation run by the NSA which gives them direct access to the data of top Internet companies, and is supposedly the top source of raw intelligence for the NSA. These slides, which originated from a top secret NSA briefing, lets the cat out of the bag in a big way, showing the companies involved (Google, Facebook, Microsoft, Apple, Yahoo, etc) and the start dates for each company's participation. If that wasn't shocking enough, another slide released by the Guardian ties both story lines together, explaining that the NSA has easy access both to raw Internet traffic as it passes over fiber optic lines, in addition to "collection directly from the servers of these U.S. service providers," followed by a list of participating companies. The slide includes the recommendation to NSA operatives that "you should use both" sources. Raw Internet traffic may provide a more expansive amount of data, yet would undoubtedly be harder to parse. The data from companies like Facebook, on the other hand, would be much easier to sort through, yet would not be nearly as expansive.
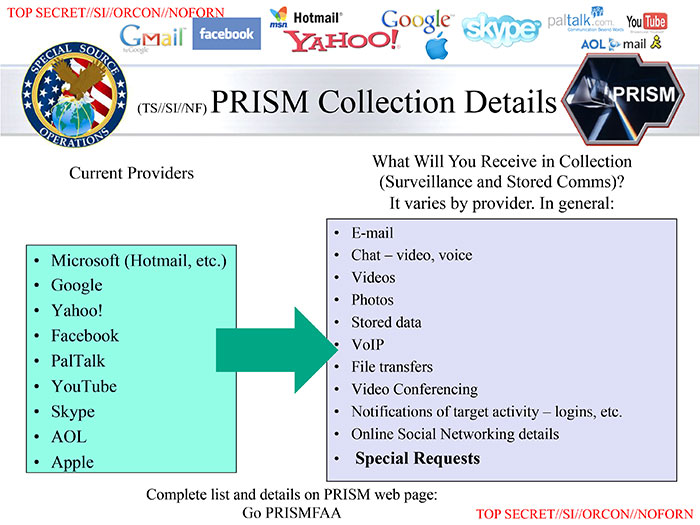
A slide from the top secret PRISM briefing which really needs no explanation
I would assume that these revelations are shocking to just about every Americans who has ever used a telephone or a computer connected to the Internet. But what exactly is the government doing with all this data? Surely, there's not enough NSA operatives to listen in to the phone calls of even a fraction of "high risk" individuals, as depicted in my cover photo from "The Lives of Others." And attempting to sort through raw Internet backbone data, or even sorting through Google's data stores, would be akin to drinking out of the world's biggest firehose. We're talking about millions of people, and yottabytes (1 yottabyte = 1 quadrillion gigabytes) of information here.
Our answer comes in the form of a construction project that has been known to the public for some time now, and given the scale of it, it's pretty hard to keep it a secret. The NSA is building a massive $2 billion data center in the middle of the Utah desert at Camp Williams as we speak, which will open in October 2013. According to James Bamford of Wired, "Once it's operational, the Utah Data Center will become, in effect, the NSA cloud. The center will be fed data from the agency's eavesdropping satellites, overseas listening posts, and secret monitoring rooms in telecom facilities throughout the U.S." You can read some technical details about the facility in that article if you're interested, but the fact of the matter is that when completed, this facility will have more than enough storage capacity and processing power to churn through the entire world's Internet traffic, parsing voice, text, and web communications. The completed Utah Data Center will become "the Death Star of the Internet," gobbling up Internet traffic from all but the most obscure corners of the web and compiling it all in one place. Sophisticated analytics will undoubtedly be a part of the process, as American citizens, and foreigners, are flagged as "high risk" targets without any human effort required.

A shot of the massive Utah Data Center under construction.
When asked to respond to this flurry of media attention over an, until now, highly classified project, President Obama gave one of the most uncomfortable press conferences I've ever seen. According to a transcript of his responses, he stated that, "When it comes to telephone calls, nobody is listening to your telephone calls. That's not what this program is about." If the data center allegations are true, we can hold Obama to his word and his statement would be true: nobody is listening to these calls, as in, no humans. Sophisticated speech-to-text software, similar to what runs Siri on your iPhone, will be parsing every call you make and tagging it, before moving on to the next call.
Now that this information is out, President Obama will undoubtedly have some damage control on his hands, and there will be a lot of complaining from media talking heads, but my guess is that nothing will actually change. What then, is the frightening next step in this program? I would assert that the next step is wide scale video surveillance and video analytics, on a scale never before achieved or attempted. When Microsoft, a PRISM program participant, announced their new Xbox One, there was some outcry over the revamped Kinect sensor. Kinect being an always-on camera with a microphone, which can see in the dark, and must be connected to the Xbox for the console to work. If this is beginning to sound like the ramblings of a conspiracy nut, I implore you to consider the revelation, several years old, that the FBI can remotely turn on the microphone of any cell phone in the United States, whether the phone was turned on or off. If they could achieve the same level of control over the Kinect sensor, which will constantly be viewing the living room of the user, the fantasy of George Orwell's "telescreen," featured in the novel 1984, would become a reality. The downside of telescreens being that they could not see in the dark in the novel - something which the Xbox Kinect sensor can do. With the release of Google Glass looming in the next year or so, things are looking grim for privacy advocates and critics of government surveillance.

The Xbox One Kinect - a device which will soon sit at the foot of many living room televisions
So what is the point of this article, if not to frighten or alarm readers? In addition to pulling together the myriad of facts from the leaks of the past news week, analyzing the details, and forming an educated opinion of what the NSA's master plan is, it is simply to inform fellow Americans. I believe that Americans have a choice to make:
- Resign to constant surveillance of the interactions they make with each other over the Internet, in addition their private information that they share with companies such as Google, under the guise of protection from terrorism
- Assert to their elected officials that these intrusions into their electronic lives are invasive and unreasonable, and that the massive surveillance dragnet created after 9/11 be dialed back significantly
The situation is troublesome enough that at least one man, Edward Snowden, the man behind these recent leaks, has come forward and exposed himself, at the risk of being prosecuted by the U.S. government. I will not applaud Snowden as a hero, but I do appreciate being told the details of these programs when the U.S. government would not have otherwise informed the public about their existence. At the very least, that has forced President Obama to address the constitutionality of the surveillance, and has rekindled the debate over warrantless wiretapping. I am not saying that these security measures are not helpful in fighting terrorism, or that they were not instituted in good faith. Every law-abiding American must simply consider the likely possibility that everything they do on the Internet, speak on a phone call, or type into a search box on Google are analyzed, tagged, and recorded by the U.S. government, and then ask themselves whether or not that is acceptable.
EDIT (6/10/2013 7:10pm EST): Since this post is getting a decent amount of traffic, I've decided to add a recently released interview with the PRISM whistleblower, Edward Snowden. This interview goes into even more depth about the capabilities of the NSA's eavesdropping systems. I've presented one chilling quote from the interview that pretty much sums it all up below:
"Any analyst at any time can target anyone... I sitting at my desk certainly had the authorities to wiretap anyone; from you or your accountant, to a federal judge, to even the President if I had a personal e-mail."
|
Older:
The revolution will not be televised - it will be streamed on Reddit |
Newer:
Xbox one, take two - How consumers forced Microsoft's next-gen hand |
